WHMCS Killer v4 Coded in Latest php version Tools Server R00t Domain Resellers Clients R00ts Clients Hosting Accounts Clients CC Clients Password NEw DEsign
WSO SHELL 2023
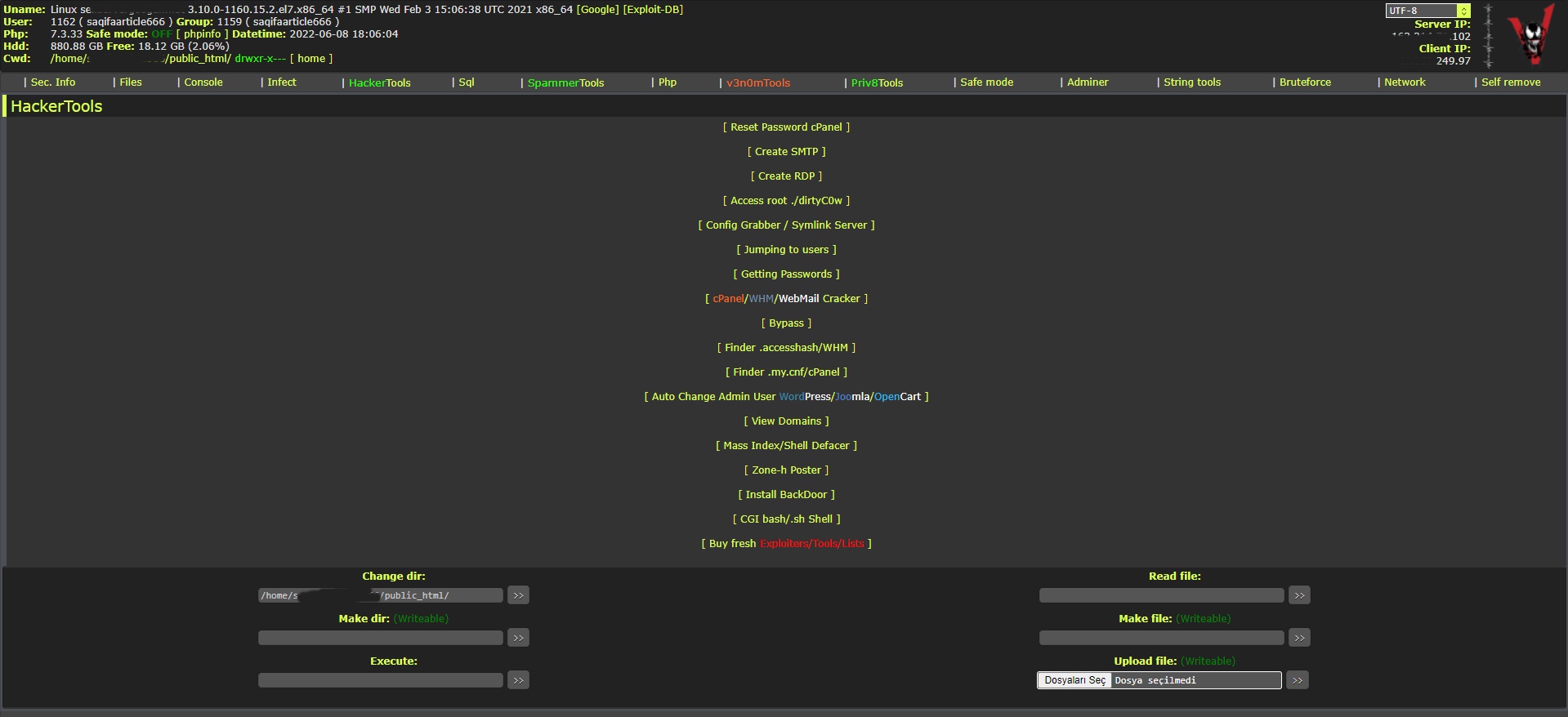
[Hacker Tools] cPanel/WHM/WebMail Cracker - Create RDP - Getting Passwords - Finder .accesshash/WHM - Finder .my.cnf/cPanel - Auto Change Admin User WordPress/Joomla/OpenCart - Zone-h Poster - Install BackDoor [Spammer Tools] Create SMTP - Create Mailer - Mail Sending Checker - Redirects - Getting Emails-List - Emails-list Filter [Other Features] Adminer - WHMCS Killer v4 - Unzip - Config Grabber[Advanced] - Server Jumping - Cgi Shell - Back Connect - Domains List [Supported] php 5.x - php 7.x - php 8.x Password:dadsec
WAnonymousFox shell 2023
FoxAuto V8 [01] Mass Reset Password cPanel [02] Mass Finder SMTP + Create SMTP [03] Mass Finder Linux/Windows, cPanel/vHosts/Root [PWD|UNAME] [04] Mass Finder Accesshash [Reseller] + .my.cnf [cPanel] [05] Mass Get Config (cPanel/vHosts) server+Config404+ConfigCFS [06] Mass Get Config + Crack cPanel/WHM [07] Mass Get Config+Upload Shell on WordPress/Joomla/Opencart [08] Mass Get Root by ./dirty [PHP/BASH] [09] Mass Get RDP from Windows server [10] Mass Get Domains-List [11] Mass Get Emails-List [12] Mass Get Config + Emails-List [13] Mass Upload Mailer [Random] [14] Mass Upload File [Random] [15] Mass Upload Index + Post in Zone-h [16] Mass Upload Scam-Page/Zip-file + UNZip [17] Mass Check if Sending mail is Working or not! [Results delivery] [18] Mass Reports replacement Olux/xLeet/Other [19] From any Shell/UPloader, MASS Upload File Shell/Mailer [20] Reset Password cPanel + Finder/Create SMTP [together] [21] [All of them together] [22] Mass Finder SMTP + Create SMTP from cPanel [23] MASS Upload File Olux/xLeet/Other Shell/Mailer from cPanel [24] Mass Upload Scam-Page/Zip-file + UNZip from cPanel [25] Mass Check if Sending mail is Working or not! [Results delivery] [26] Mass Reports replacement Olux/xLeet/Other from cPanel [27] Mass login WordPress/Joomla/Opencart/Drupal + UPload Shell
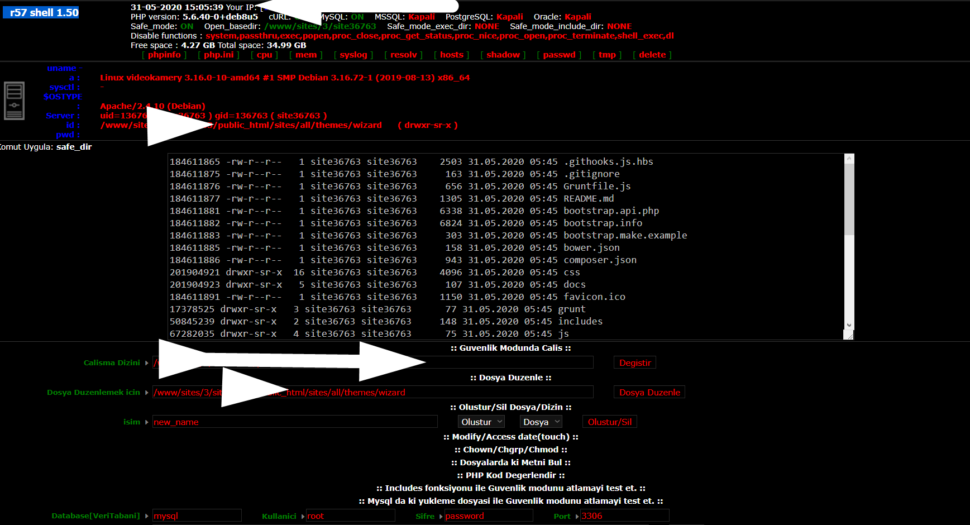
Wr57 shell txt
visit the most interesting R57 pages, well-liked by users from your country and all over the world, or check the rest of r57.biz data below. R57.biz is a website, reported to be malware-infected or hijacked, so you should stay away from it until the problem is resolved. We found that English is the preferred language on R57 pages. Their most used social media is Facebook with about 93% of all user votes and reposts.
: This article is for informational purposes only and does not promote or endorse piracy or copyright infringement. We encourage readers to respect the intellectual property rights of creators and opt for legitimate channels to access their favorite movies.
Uriyadi 2 Tamilyogi Download: A Comprehensive Guide** Uriyadi 2 Tamilyogi Download
Tamilyogi is a popular online platform that allows users to download and stream a wide range of Tamil movies, including new releases and classic films. The website has gained a massive following among Tamil movie enthusiasts, offering a vast collection of films in various genres. However, it’s essential to note that Tamilyogi operates in a gray area, and its legitimacy is often questioned due to copyright concerns. : This article is for informational purposes only
Uriyadi 2, a highly anticipated Tamil movie, has been making waves in the film industry with its thrilling action sequences and captivating storyline. The movie has garnered significant attention from fans, and many are eager to watch it. If you’re one of those fans searching for a way to download Uriyadi 2, you’ve likely come across the name Tamilyogi. In this article, we’ll explore the world of Tamilyogi and provide a step-by-step guide on how to download Uriyadi 2 from the platform. The website has gained a massive following among
Downloading Uriyadi 2 from Tamilyogi requires caution and awareness of the potential risks. While the platform offers a vast movie library, it’s essential to prioritize your online safety and consider alternative, legitimate options. If you still choose to use Tamilyogi, follow the steps outlined above and take necessary precautions to protect your device and personal data.